Digital Forensics
Digital Forensics is a highly specialised and rapidly growing field of investigation. Given the prevalence of technology in the world today, the need to investigate the activities conducted using technological devices is becoming more relevant and useful.
Technology is integrated into our daily lives, personally and professionally. As a result, the data on the devices we wear, carry, and interact with can provide useful information when examined during an investigation.
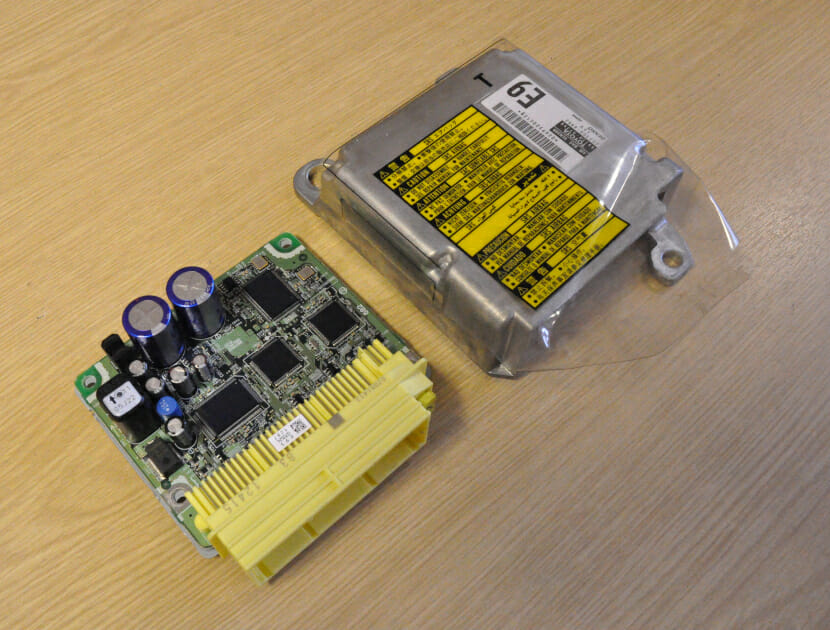
Our experts are qualified and experienced Digital Forensic Investigators who complete each stage of Digital Forensic Investigation (DFI) models whilst conforming to ACPO guidelines and ISO standards. This requires using various industry standard Digital Forensic acquisition and analysis tools to acquire, analyse, identify, and report on electronically stored information (ESI) from various devices such as servers, desktop computers, laptops, tablets, mobile phones, CCTV/DVR units, Sat Navs, USB storage devices and motor vehicles. The investigations can be conducted on-site, remotely, or in a Hawkins laboratory, depending on the circumstances.
If there are technological devices involved in your matter and you want to know what relevant information they may hold, you need a Digital Forensic Investigator. Hawkins can provide an expert who is familiar with all aspects of a case and can offer clarity and answers to your questions.
Hawkins’ Digital Forensic Investigators have knowledge of, and experience working with, the following types of:
Devices:
- Servers
- Desktop computers
- Laptops
- Tablets
- Mobile phones
- CCTV/DVR units
- Sat Navs
- Motor vehicles
- USB storage devices
Operating Systems:
- Windows
- MacOS
- Linux
- iOS
- Android
- Other proprietary operating systems
Law:
- Criminal
- Civil
- Family
WHY APPOINT A DIGITAL FORENSIC INVESTIGATOR?
Hawkins’ Digital Forensic Investigators have a plethora of knowledge and experience within Digital Forensics, having been instructed on several high-profile criminal and civil litigations as well as a public inquiry. Each Investigator undertakes rigorous technical and expert witness training, as well as adhering to best practice guidelines, standards, processes and procedures at all times. We have the technical knowledge and experience to tell you how a technological device was involved in a matter and what relevant information it contains.
- We have laboratories and equipment designed specifically for Digital Forensic investigations.
- Our experts are knowledgeable in a wide range of areas and can investigate all aspects of a Digital Forensic investigation, meaning that you will probably only need to instruct one expert, rather than several.
- We will provide answers and help you to understand questions such as:
- What events occurred during a specific timeframe?
- What telephone calls and messages were sent and received?
- Was any data deleted?
- Was data transferred to a USB storage device?
- Who sent an email?
- What websites were visited?
- What search terms were searched?
- What are the created, last modified and last accessed dates and times of the document?
- Who authored the document?
- What was the location of the device?
- Was there an email phishing attack?
- We can act as an independent or a single-joint expert witness.
- We produce reports suitable for use in tribunals, mediation, litigation and court.
- We provide consultancy advice to prevent similar events happening again in the future.
- If removing a risk entirely is unavoidable, we advise on steps to take to mitigate the risk and reduce the potential damage resulting from an incident.


Examples of Typical cases
If you would like to know if we can help, please fill out our enquiry form or give us a call for a free consultation. The list below provides a few examples of cases which we investigate regularly or have investigated in the past.
- Murder, manslaughter or assault
- Sexual offences
- Fraud and insurance fraud
- Bribery
- Intellectual property theft
- Fires and explosions
- Employment tribunals
- Breach of contract
- Negligence
- Family disputes
- Road traffic collisions (RTCs)
HOW DOES HAWKINS CONDUCT DIGITAL FORENSIC INVESTIGATIONS?
1
Consultation
We like to speak to you before we conduct any work, to establish how we can add value to the case. These discussions help us to understand your requirements, as well as determining how much information is already available. We are also happy to provide you with an estimate of the cost of conducting a forensic investigation.
2
Conclusion
Once our examination is complete, we will discuss our findings with you and prepare a report containing a detailed account of our investigation, conclusions, and where appropriate, further work or advice.
SPEAK TO ONE OF OUR EXPERTS
Related areas of expertise
Cyber, Digital & Technology
As the world continuously strives to become ever more digital, it brings with it the requirement for appropriately qualified and experienced experts who are able to investigate and report on the technologies, their infrastructure and their data.
Data Recovery
Given the prevalence of technology in the world today, there is a huge increase in data being lost, deleted, or corrupted. We truly understand the importance of data and the personal and commercial consequences of losing access to it.
Video Analysis
Closed Circuit Television (CCTV) systems and portable video recording devices are ubiquitous. Video recordings can provide definite and compelling evidence, often entirely in isolation.
Photogrammetry
Photogrammetry is the process of obtaining reliable spatial information from 2D still photographs. Photographs often are the best available source of evidence in ascertaining the precise height, position, and orientation of objects in an incident scene.
Download our latest Brochure
 Italiano
Italiano